There's nothing more dangerous than a bored engineer with a screwdriver, and hell hath no fury like a security researcher scorned. Last month, Security researcher Chaotic Eclipse (aka Nightmare-Eclipse) published two zero-day exploits, BlueHammer and RedSun, that made Windows Defender offer up system administrator privileges. They did this after their disclosure reports were allegedly dismissed by Microsoft's security team, resulting in a vendetta of sorts. Eclipse has now done it again, posting two new zero-day exploits, the first one an extremely serious BitLocker exploit named Yellow Key that grants full access to a locked drive. The second one, GreenPlasma, doesn't have a complete proof-of-concept (PoC), but it allegedly performs a local privilege escalation and gains system-level access. Given Eclipse's track record, it's a fair bet that it works as advertised.
YellowKey can be triggered simply by merely copying some files to a USB stick and rebooting to the Windows Recovery Environment. We tested this ourselves, and sure enough, not only does it work, it bears all the hallmarks of a backdoor, down to the exploit's files disappearing from the USB stick after it's used once.
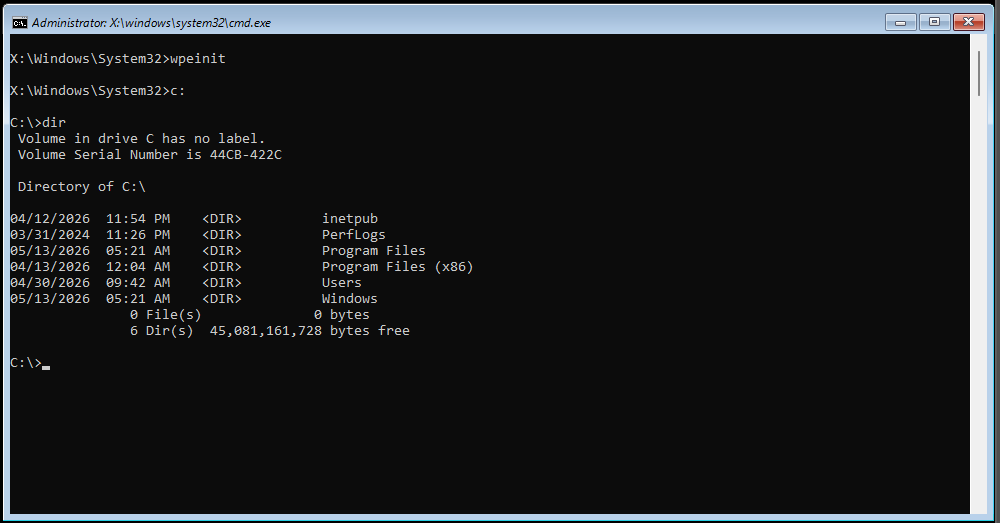
To say that this is dangerous is an understatement. Not only is it an immediate concern as BitLocker cannot be trusted for encrypting drives, but the way the exploit executes and its files disappear also raises very uncomfortable corporate and/or political questions. YellowKey also reportedly works in Windows Server 2022 and 2025, but not in Windows 10.
BitLocker protects millions of machines worldwide across home, enterprises, and governments, especially as it's enabled by default in Windows 11. As far as we can tell, a drive can't be taken from machine Alice and opened in machine Bob because the encryption keys are in Alice's TPM, but it's not hard to just up and steal a laptop, mini-PC, or even desktop.
Eclipse notes that using a full TPM-and-PIN setup doesn't help, as apparently, they have a variant for that scenario that they haven't published a PoC for. They also state the vulnerability is well-hidden, and that they "could have made some insane cash selling this, but no amount of money will stand between me and my determination against Microsoft."
As for GreenPlasma, it's supposed to get an attacker full system-level access (even higher than administrator) by manipulating the CTFMon process into placing a crafted memory section object — a slice of memory that can be shared between processes or mapped to a file — in any Windows' Object Manager section the SYSTEM user has write access to, bypassing regular access controls.
From thereon, the exploit code can get access to regions of memory they're not meant to and leverage that for any number of shenanigans, the most obvious one being getting full system access. This is bad enough for a desktop system, as any program can get full access, but it's particularly bad for server environments, where any regular user can get control of the server and, by extension, everyone else's data.
Meanwhile, as of this writing, there is no official response from the company about YellowKey or GreenPlasma. BlueHammer has already been patched, and Chaotic claims that Microsoft silently patched RedSun, but there's no official word on that either.

Follow Tom's Hardware on Google News, or add us as a preferred source, to get our latest news, analysis, & reviews in your feeds.