Part of the Big Tech's War on Users series
Proton. The name comes up every single time someone asks where to go after Google. After Gmail. After that moment you realize free email means you're the product. For years, the privacy community has had one reliable answer: Proton. Swiss company. Swiss servers. Swiss law. Outside US jurisdiction. Safe.
I'll be honest — I believed it too. It's a super compelling story.
It's also not the whole story.
Before we go further I want to be straight with you about something. This piece is going to read differently than most things I write here. Less sass. Less sarcasm. More documentation. More plain language. And there's a specific reason for that.
Because this one matters more.
The people this affects aren't just annoyed subscribers who got hit with a price hike or a feature removal. They're people who made real decisions based on what Proton told them. Journalists. Activists. Lawyers. Ordinary people in countries with complicated relationships with the US government. A Swiss citizen who did everything right. An EU user who thought GDPR had them covered. Someone who switched specifically because they were scared and Proton told them they'd be safe.
And to be clear — this isn't about condoning anything illegal. If you're doing something that warrants a government investigation, that's a you problem and frankly not what this is about. This is about something more fundamental. When a company tells you one thing and their own legal documents say another — that's a problem regardless of who you are or what you're doing. An upstanding citizen deserves to know the product they're trusting with their private life isn't what it claimed to be. Full stop. The legality of your behavior doesn't change the legitimacy of the deception.
And every single source in this piece is something Proton or LiveKit published themselves — or a federal court record.
That's the other reason to keep it straight. Because when the receipts are this good you don't need to editorialize. You just need to line them up and let people read.
Let's do that.
Before you jump in — and before anyone starts composing their reply about how wrong I am — I'm asking one thing. Read the whole piece. Not the first section. Not the first section and a skim. The whole thing.
Because the Setup section that comes next is going to sound like I'm making Proton's case for them. That's intentional. I want you to feel the full weight of what was promised before we look at what was actually built underneath it.
If you read the Setup and stop there to tell me I'm wrong — you've just proven you're more invested in the brand than the truth. And that's kind of the whole point.
Still here? Good. Let's talk about what Proton told you.
THE SETUP: What Proton Told You
The pitch was simple and it was good. Good enough that millions of people bought it. Good enough that it became the default recommendation across every privacy forum, every de-google guide, every "okay but what should I actually use" thread on Reddit and Mastodon.
Here it is in their own words. All of these are linked. Click them.
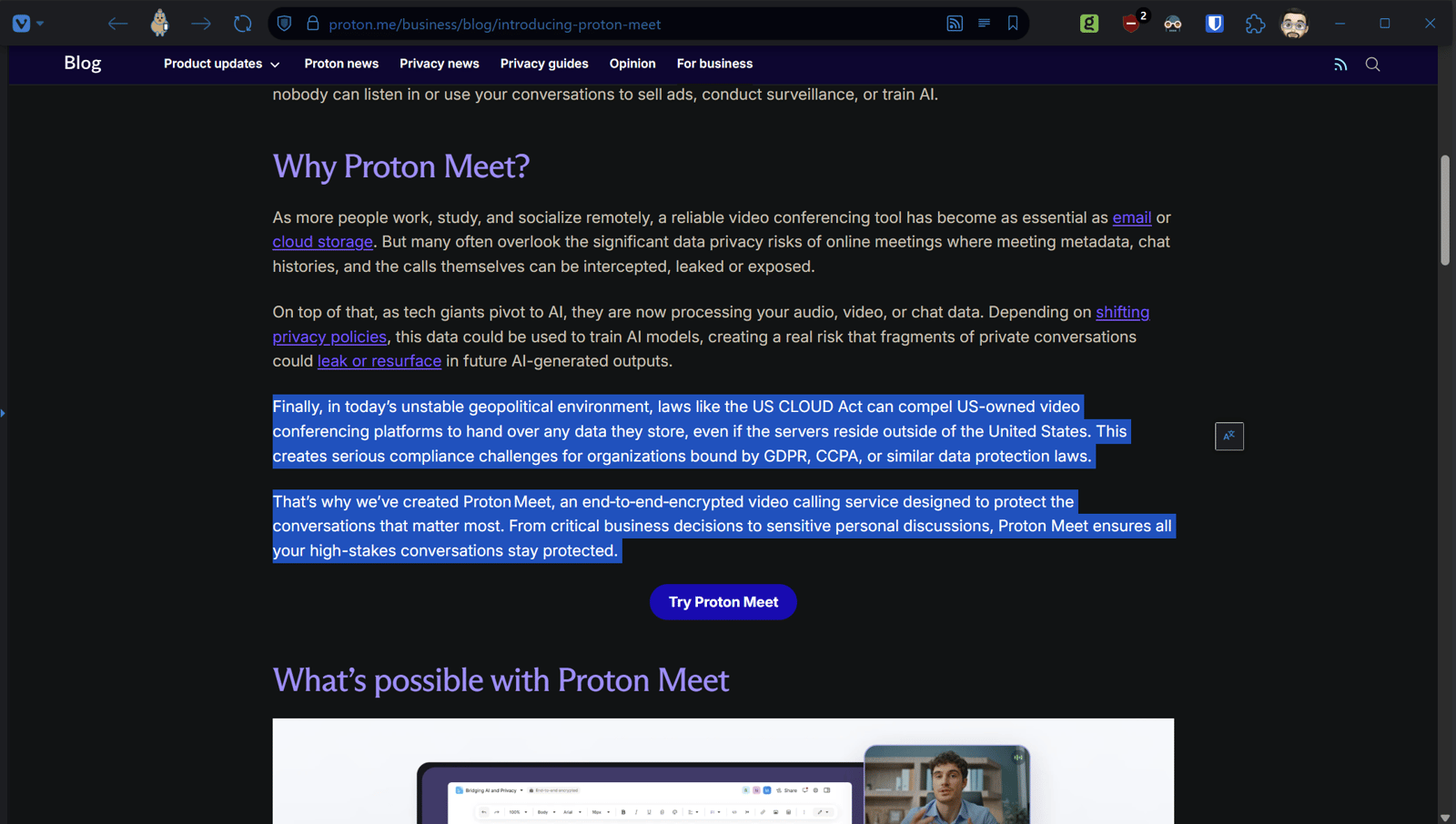
In their Meet launch blog — the one announcing the product this whole conversation started with — Proton cited the US CLOUD Act, which can compel American platforms to hand over stored data regardless of server location, as the explicit reason they built Proton Meet. The CLOUD Act was the problem. Proton Meet was the solution.
Their business page promises that nobody can ever access calls — listing third parties, AI models, advertisers, hackers, government agencies, and Proton themselves as entities categorically locked out.
Their own blog stated flatly that as a Swiss company they are not governed by US laws.
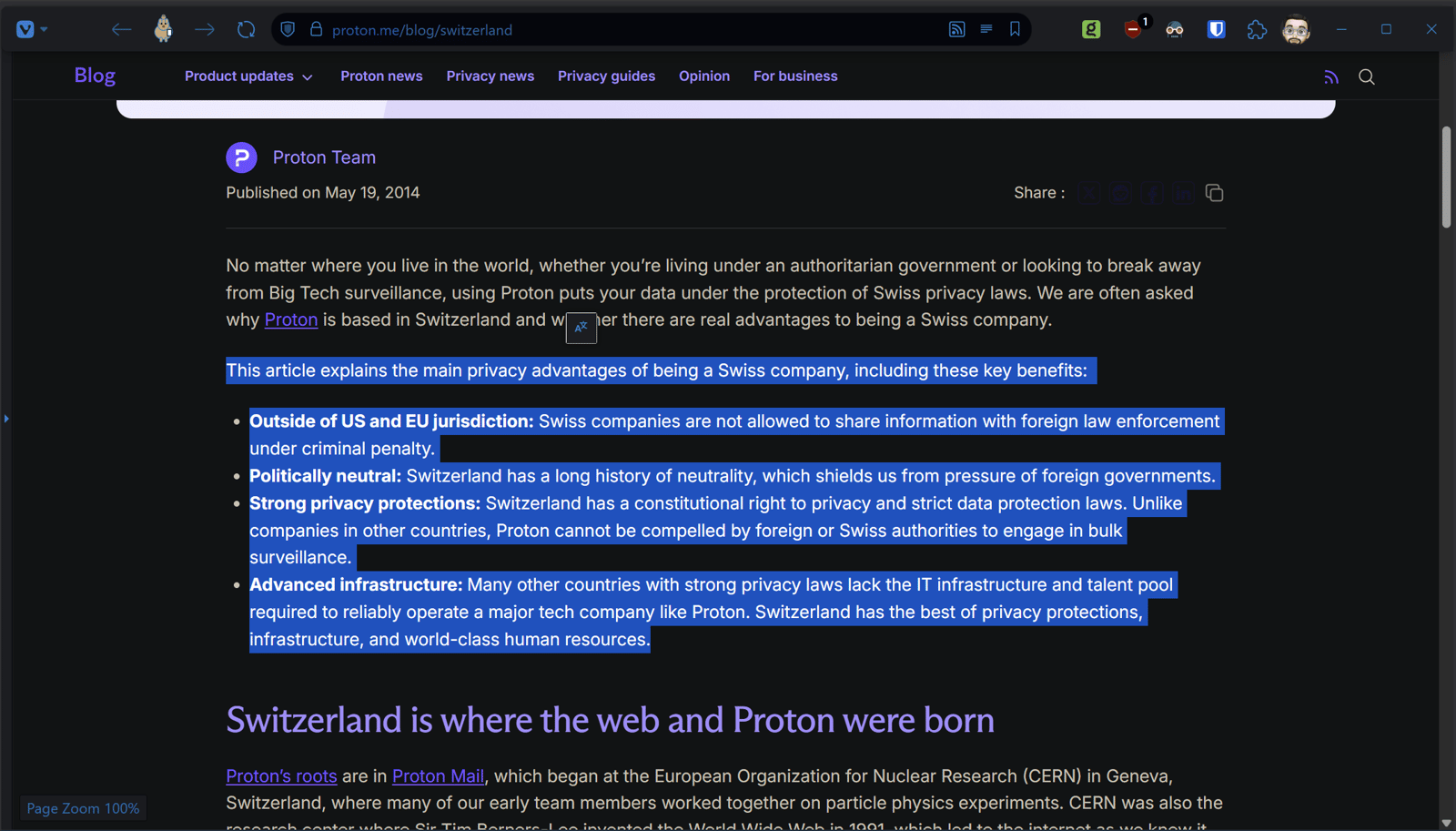
Their Switzerland explainer blog — a whole post dedicated to why being Swiss matters — claimed being outside US and EU jurisdiction means Swiss companies face criminal penalties for sharing information with foreign law enforcement. Published May 2014. Still live. Over a decade of that claim sitting there.
Their Drive security page described Switzerland as politically neutral, outside US and EU jurisdiction, and not party to any Five Eyes or Fourteen Eyes intelligence sharing agreements. And under Article 271 of the Swiss Criminal Code, Proton is prohibited from sharing data with foreign authorities.
Their VPN business page described Proton as operating outside EU, US, and UK legal jurisdiction under some of the world's strongest privacy laws. On the same page, in the Anti-censorship section, they note their technology uses third-party networks like AWS. Both statements. Same page. No acknowledgment of the contradiction.
Their privacy page states the services are operated from Geneva and therefore governed by Swiss law.
And then there's this one. This one deserves its own moment.
Proton doesn't just market to regular people tired of Gmail. They have a journalist discount program. A dedicated page for newsrooms. Blog posts about protecting press freedom. They specifically, deliberately, and repeatedly told journalists — people whose sources can go to prison, people whose communications can get someone killed in the wrong country — that Swiss jurisdiction meant foreign subpoenas couldn't touch them.
Their journalist page explicitly told newsrooms that as a Swiss company they cannot legally comply with any foreign subpoenas and that data sits outside US or EU jurisdiction. "Get our discount for newsrooms." Button and everything. Still live as of this writing.
They didn't stumble into that claim. They put it on the page specifically designed to get journalists to pay for a subscription. To trust them with their sources. To use Proton Meet for sensitive calls. To store documents in Proton Drive. To communicate through Proton Mail.
Think about what that means for a moment.
A journalist in Turkey. A source inside a government agency in Brazil. A whistleblower communicating with a reporter covering US defense contractors. A lawyer and client discussing a case involving federal agencies. All of them making decisions — real decisions with real consequences — based on that promise.
People whose sources don't just risk prison. In some parts of the world they risk disappearing entirely. A dissident. A human rights worker. Someone documenting atrocities who needed to know their communications were genuinely protected before they trusted anyone with information that could get them killed.
All of them potentially on a call routed through Oracle infrastructure in Phoenix, Arizona. Through a California company that explicitly cooperates with US law enforcement. Under a Terms of Service that for US users routes disputes through the Federal Arbitration Act.
Not because they didn't do their research. Because they did. And Proton's own page told them they were covered.
That page is still up.
That's the promise. Stated clearly. Repeatedly. Across multiple products. In their own voice.
Now let's look at what they actually built.
THE INFRASTRUCTURE LAYER: What's Actually Under The Hood
Let's walk through the infrastructure layer piece by piece. Every claim here links directly to the source document. Click them. Verify them yourself. That's the point.
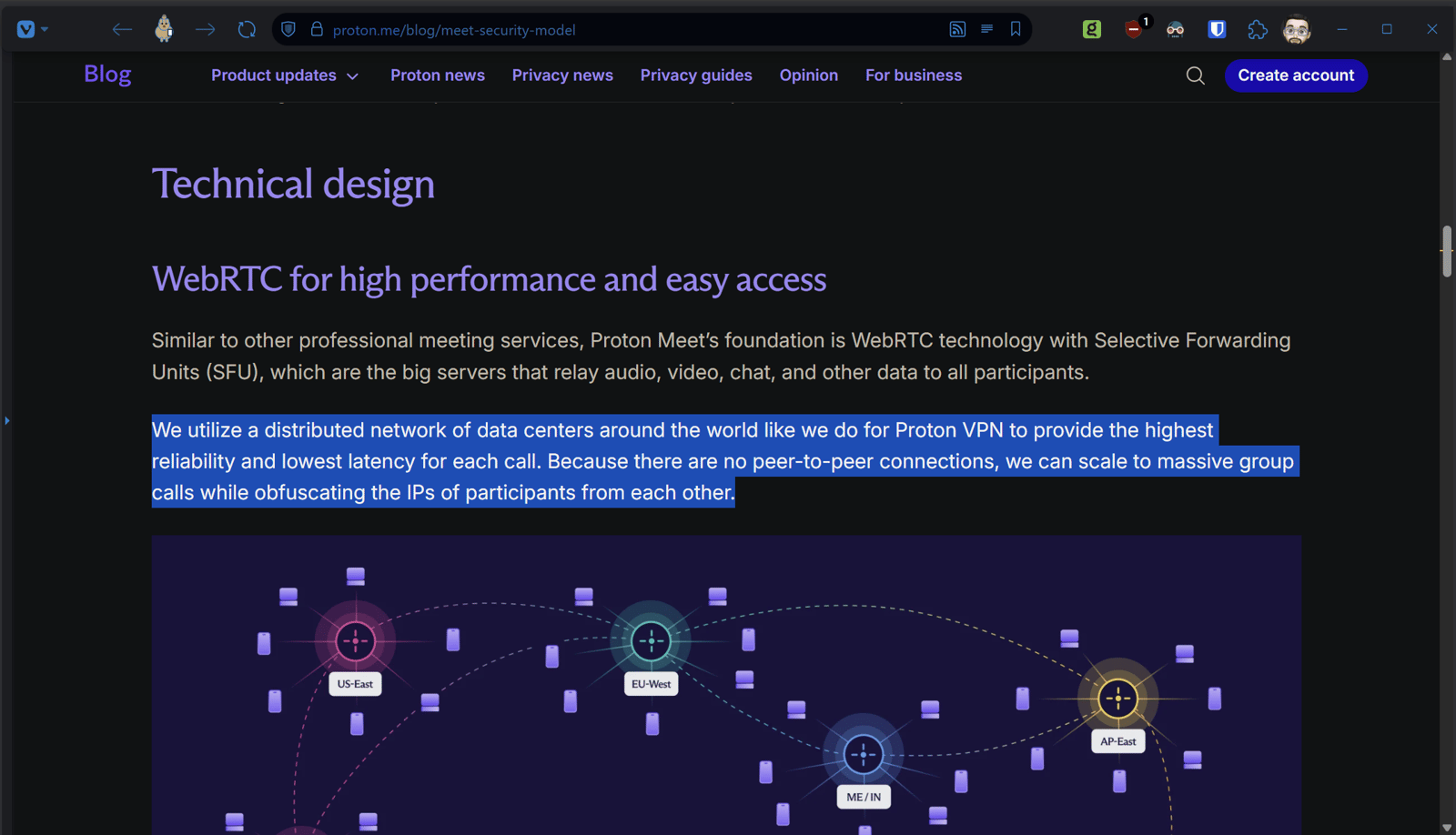
First — LiveKit Cloud as the backbone of Proton Meet. This isn't speculation or reverse engineering. Proton's own Meet privacy policy — last modified March 31st, 2026, the day of launch — discloses that LiveKit Cloud handles the transmission and routing of all video conferencing data. The same policy claims the infrastructure "cannot access any meaningful user information." We'll come back to what "meaningful" means in a moment.
Their words. Their policy. Their product.
Before we go further — Proton's older products, Mail, Drive, and VPN, do run on infrastructure Proton owns in Switzerland, Germany, and Norway. That's documented and verifiable and we're not going to imply otherwise. Meet is different. Meet is the new product. And Meet is what they chose to build on LiveKit. That choice is the story.
Also worth noting: Proton's own Workspace launch materials, published alongside Meet, claim "Proton also operates our own infrastructure which is independent from Big Tech" and that they "can't be compelled by laws such as the US CLOUD Act." Their Meet security model blog similarly implies they operate their own distributed data center network. Those claims were published while Meet was already running on LiveKit. The marketing and the architecture were not in the same conversation.
Their abortion and data privacy blog — the one specifically arguing why US jurisdiction makes American companies dangerous — explicitly invokes Lavabit and states "we reject all data requests from foreign agencies." Published while the compliance numbers were quietly accumulating in the transparency report.
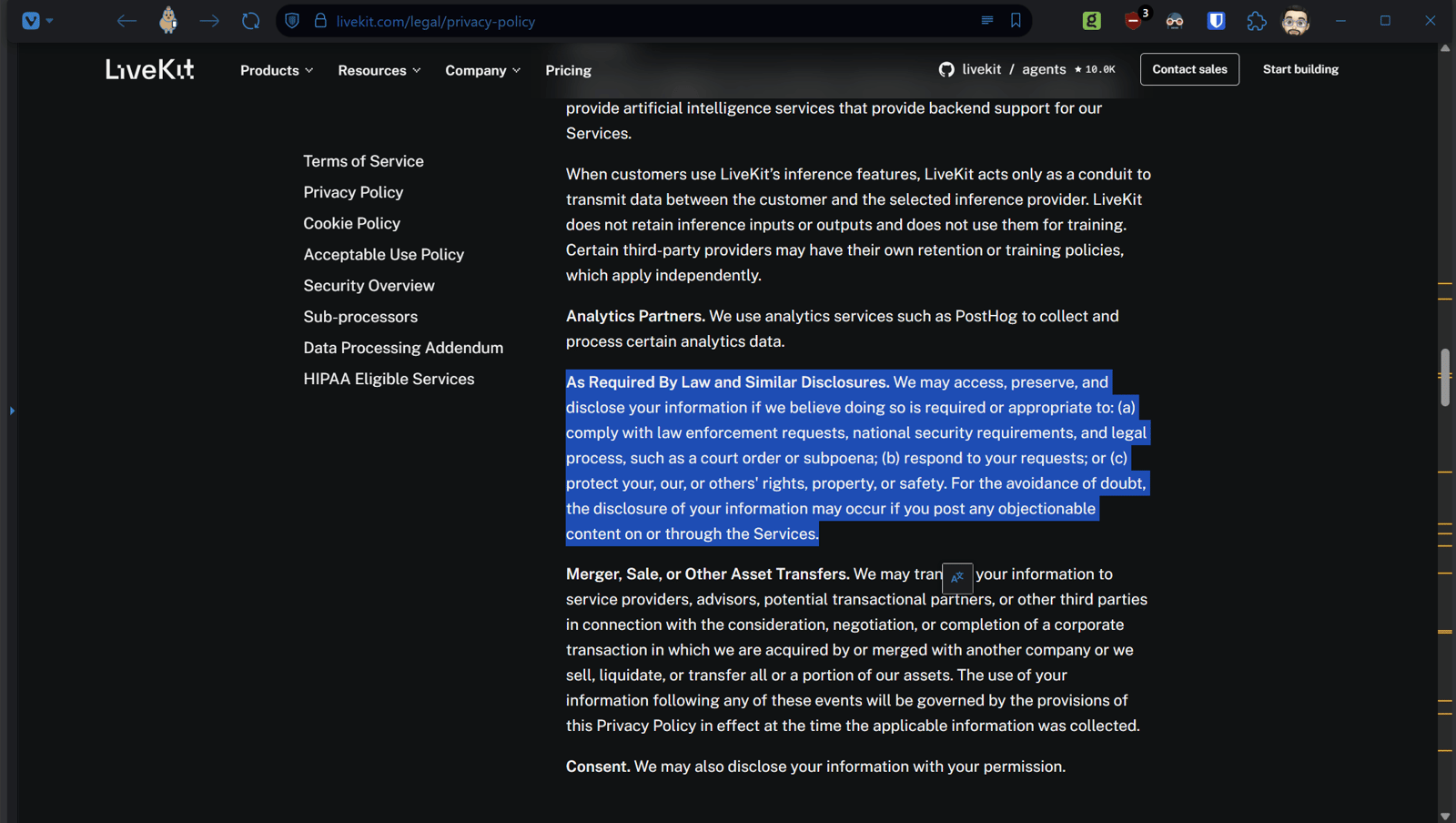
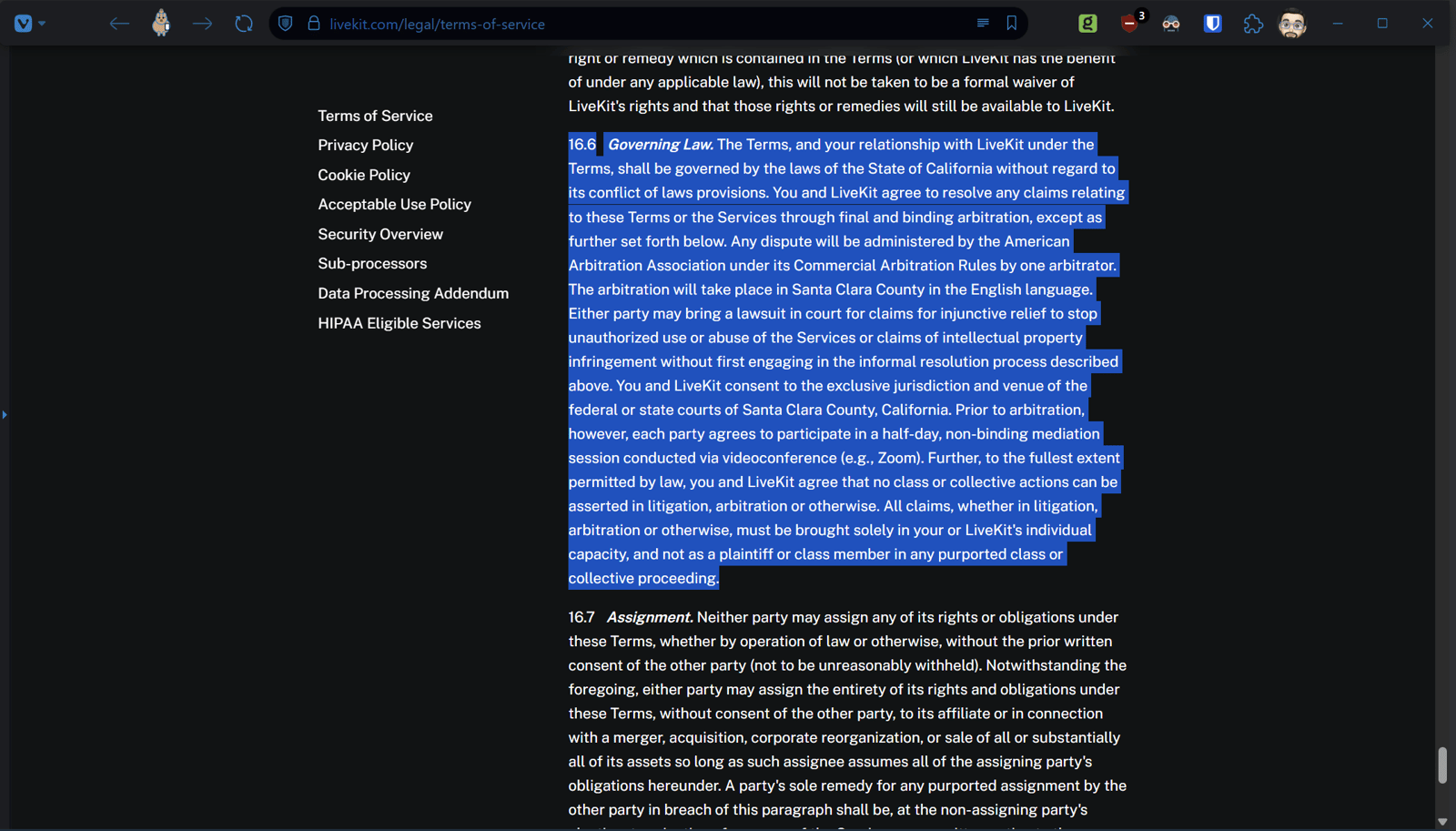
Second — LiveKit Cloud's legal jurisdiction. LiveKit's own terms of service specify that all disputes are governed by the laws of the State of California, with venue in the federal or state courts of Santa Clara County. California law. American Arbitration Association. Class action waiver. All of it. Their privacy policy explicitly states they will cooperate with law enforcement requests, national security requirements, and legal process including court orders and subpoenas.
California. Not Geneva. Not Zurich. Santa Clara County.
Let that land for a second.
The product created specifically to escape US jurisdiction. Built on US infrastructure. Incorporated in California. Governed by California law. Subject to FTC jurisdiction. With an explicit statement in their own terms that they will cooperate with law enforcement on legal requests — including national security requests. That is the precise scope of the CLOUD Act. The exact thing Proton said they built Meet to escape.
That's not an interpretation. That's not reading between lines. That's LiveKit's own terms of service and Proton's own Meet privacy policy. Two documents. Both public. Both verifiable in about thirty seconds.
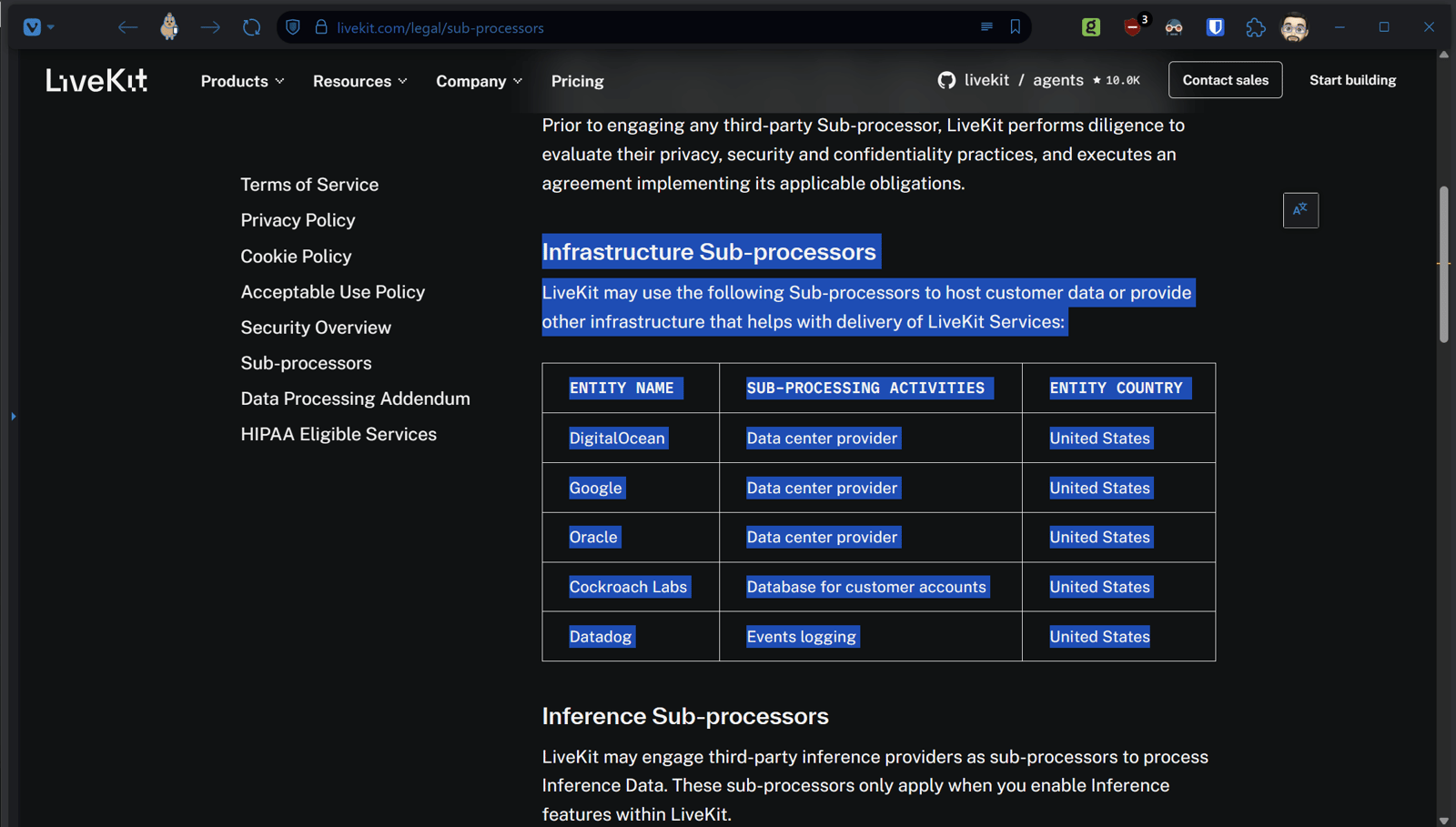
Third — the sub-processor chain. LiveKit's own sub-processor list confirms every company handling your data in that chain:
- DigitalOcean — US company
- Google — US company
- Oracle — US company
- Cockroach Labs — US company
- Datadog — US publicly traded company
Zero non-US companies. One hundred percent American infrastructure chain.
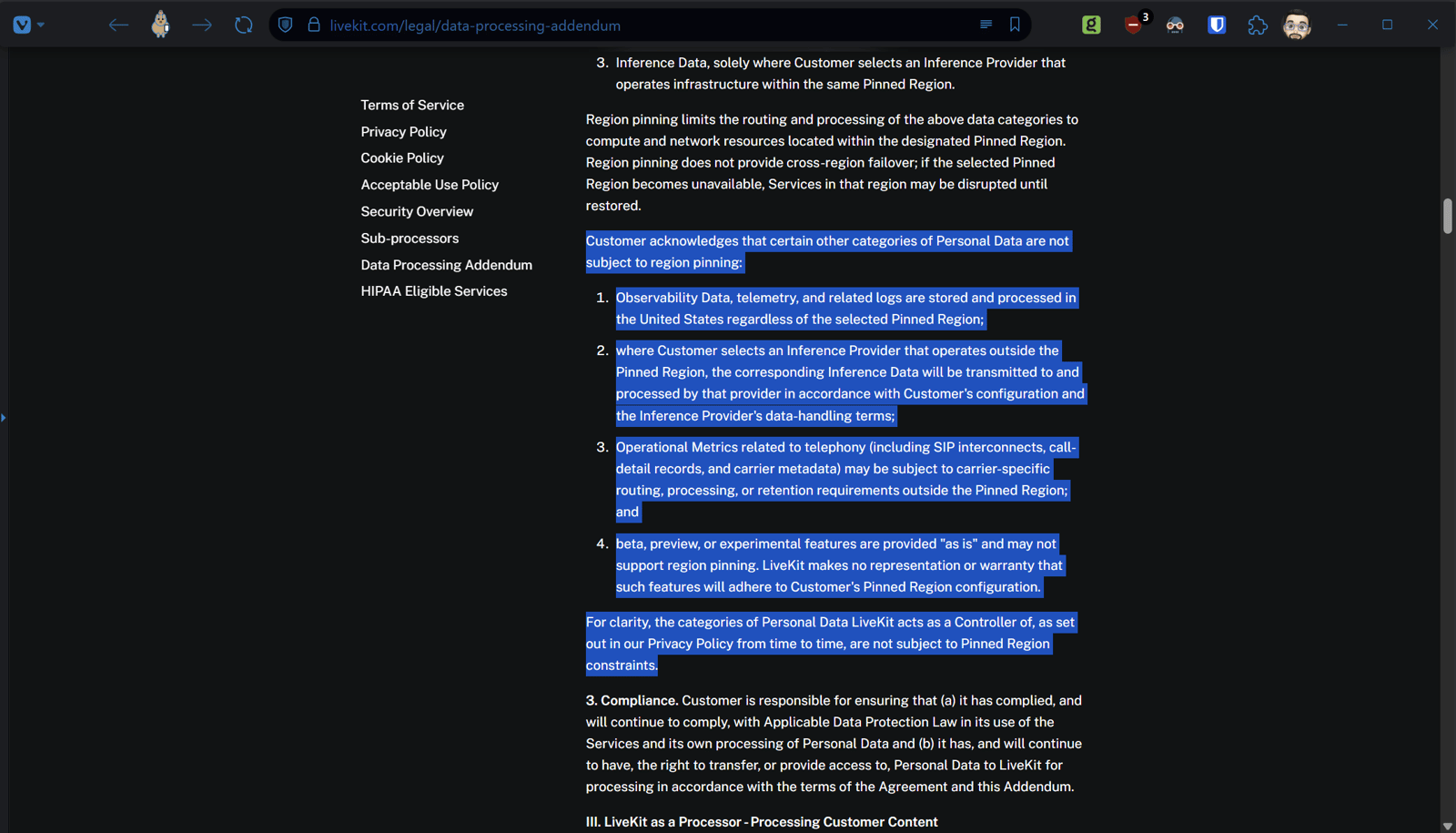
Fourth — and this one has no configuration workaround. LiveKit's Data Processing Addendum states that telemetry and logs route to the United States regardless of any regional configuration.
Regardless. Of. The. Selected. Region.
It doesn't matter if Proton configured EU routing. Your call metadata, connection records, and telemetry go to the United States in every configuration. Every time. No exceptions.
Fifth — LiveKit's legal status regarding your call records. Under their own DPA, LiveKit acts as an independent Controller for Operational Metrics — which includes call detail records, connection timestamps, and IP addresses. Independent Controller means Proton's own data agreements don't cover this data. LiveKit can hand those records to US law enforcement without notifying Proton. Proton cannot prevent it.
This is what "cannot access any meaningful user information" is working around. Proton's policy isn't lying about the encryption. But it's characterizing call detail records, IP addresses, and connection timestamps — the exact data a federal investigation runs on — as not "meaningful." LiveKit's own DPA categorizes those same records as Operational Metrics they retain as independent Controller. A Domestic Terrorism squad would find them extremely meaningful. That gap between "meaningful" in Proton's policy and "meaningful" in a federal affidavit is where real people's privacy lives and dies.
Sixth — the .com domain. The agency that controls the entire .com top level domain is ICANN. Based in Los Angeles, California. Verisign, which operates the .com registry, is also a US company. Proton acknowledged this themselves — noting the US government could theoretically seize protonmail.com because of Verisign's US jurisdiction. They knew. They said so publicly. And then built Meet entirely on US infrastructure anyway.
If you want to verify this at the network layer rather than just taking documents at face value — researcher Sam Bent did exactly that during a live Proton Meet session on launch day. His full technical investigation documents active connections to Oracle Cloud infrastructure in Phoenix, Arizona and Amazon EC2 in Oregon during a real call. The IP addresses. The ASN lookups. The browser console output naming LiveKit's own JavaScript SDK by filename. The Content Security Policy headers whitelisting LiveKit domains baked directly into meet.proton.me. His findings were subsequently confirmed independently by Steiger Legal — a Swiss law firm — who reviewed the same documents and reached the same conclusions.
This isn't a theoretical vulnerability. This is the architecture. Documented. Verified. Linked. Confirmed by a Swiss law firm.
And as of this writing Proton has not publicly responded.
The rest of the Proton suite — Mail, Drive, VPN, Pass, Calendar — each has its own infrastructure, its own sub-processors, its own legal agreements. Those older products do run on infrastructure Proton owns in Switzerland, Germany, and Norway. We're not going to imply otherwise. What we will note is that even within those products there are threads worth pulling. Their own VPN business page acknowledges using AWS infrastructure specifically for anti-censorship routing — right next to the card claiming Swiss privacy and operating outside EU, US, and UK legal jurisdiction. Both on the same page. Neither acknowledging the other. Where US infrastructure appears in any Proton product, what data touches it, and what legal framework governs that specific data is the question worth asking for each product individually.
You now know what to look for. And you know where Proton's own documents live.
But before you go looking — there's something else you need to read. Because the infrastructure is only part of the picture. The other part has been sitting in Proton's Terms of Service the whole time. Quietly. In plain English. Waiting for someone to line it up next to their marketing copy.
Let's do that now.
THE LEGAL LAYER: What Proton's Own Documents Say
Proton's marketing has one consistent message regardless of which product page you're reading, which blog post you're viewing, or which social media post brought you to them:
Swiss company. Swiss law. Swiss protection. Outside US jurisdiction.
They've said it so many times, in so many ways, across so many years, that it has become received wisdom in the privacy community. You don't even question it anymore. It's just true. Everyone knows it.
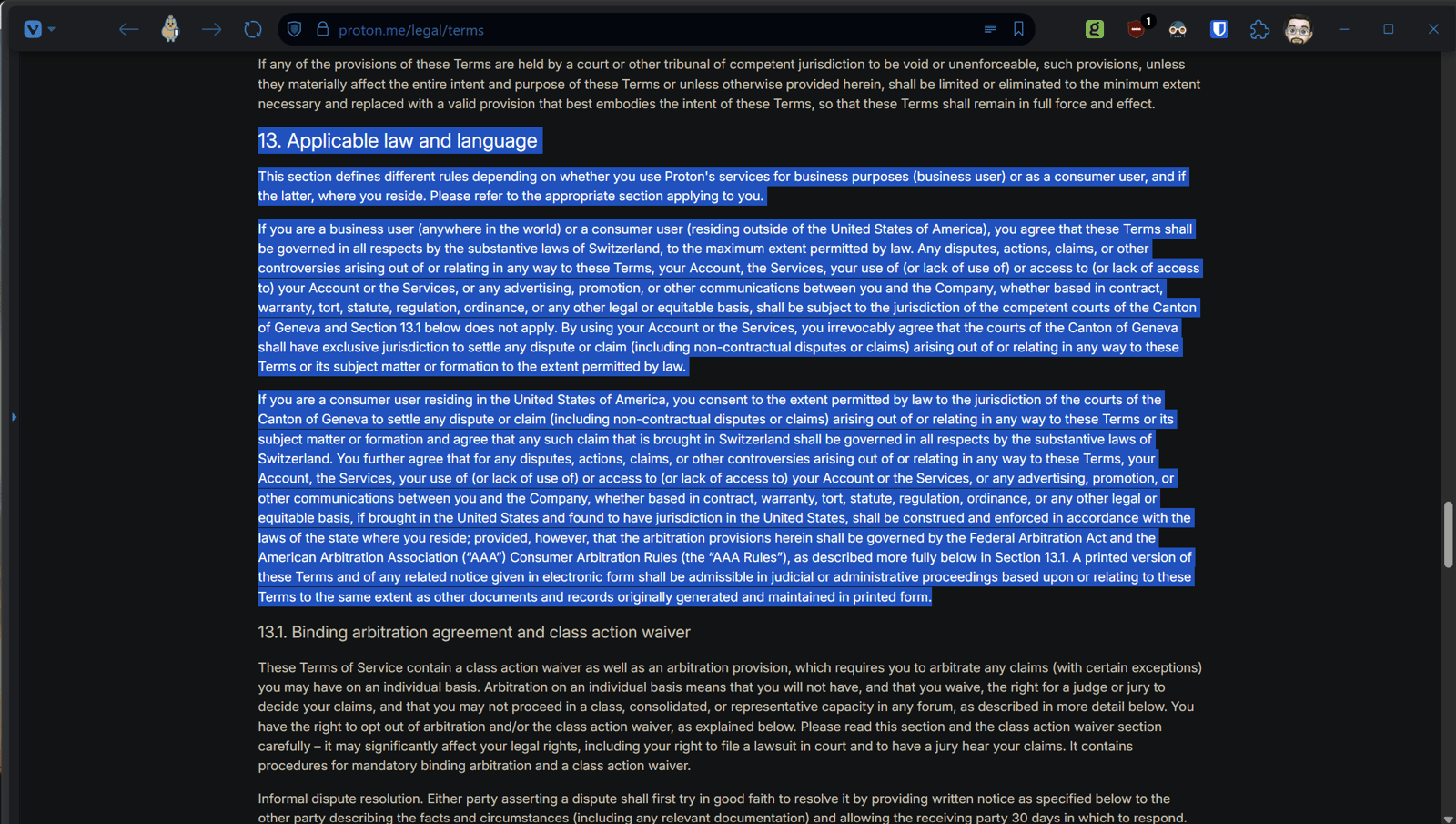
Except Proton's own Terms of Service tells a different story. And not in the fine print. In a dedicated section. With specific language. That someone deliberately wrote and a team of lawyers reviewed before it went live.
Read it yourself. Section 13. Last modified March 31, 2026.
For business users anywhere in the world, and for consumer users outside the United States — Swiss law governs. Geneva courts have jurisdiction. That's the Swiss protection they're selling.
Now here's the part that doesn't make the marketing copy.
For US consumer users, Proton's own Terms of Service specifies that disputes brought in the United States are governed by the laws of the state where the user resides, with arbitration governed by the Federal Arbitration Act and American Arbitration Association rules.
Read that again.
A US user of a product marketed specifically as being outside US jurisdiction has agreed — in Proton's own Terms of Service — to resolve disputes under US federal arbitration law.
But it goes further. That same section includes a class action waiver. US users cannot band together to sue. Each person arbitrates individually. Under US rules. Under a US federal statute. With a US arbitration body.
This isn't buried. It isn't hidden. It's in the Terms of Service of a company whose own blog stated flatly they are not governed by US laws.
Those two statements cannot both be true. Proton published both of them.
And here's the thing about jurisdiction that Proton's marketing doesn't mention. It isn't a switch you flip. It isn't a flag you plant. It's a legal determination based on connections — and the moment you have meaningful connections to a country, that country can make a credible claim over the relevant activity.
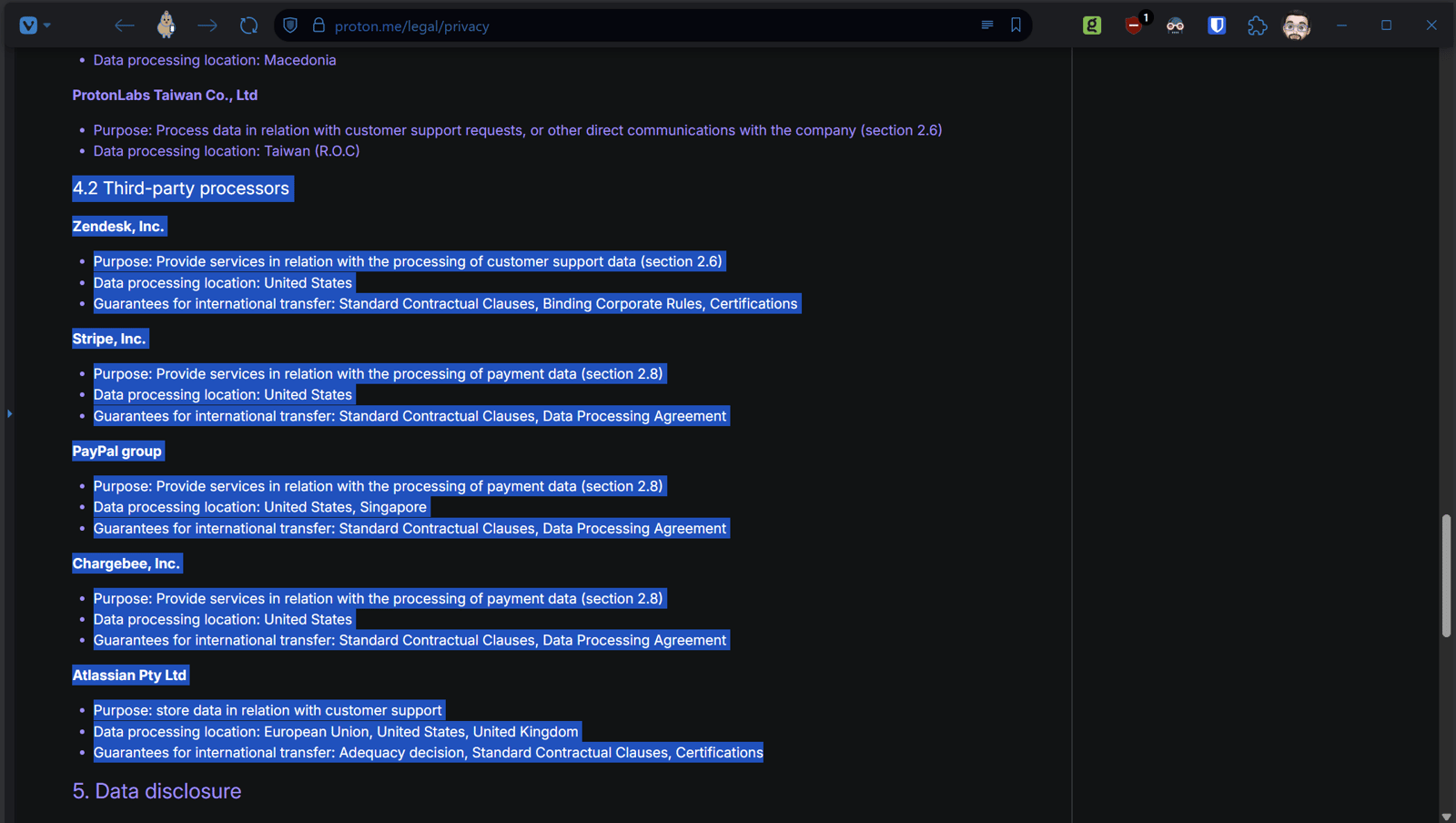
Proton's connections to the United States aren't marginal. A ToS with explicit US jurisdiction clauses they drafted themselves. Payment processing through Stripe and Chargebee — both US companies. LiveKit — a California company under contract for core Meet infrastructure. A US user base in the millions. App distribution through Apple App Store and Google Play. The .com domain under Verisign and ICANN.
Dipping a toe into US jurisdiction doesn't allow selectiveness about which laws apply or which agencies can come knocking. Any lawyer will tell you. Proton's own lawyers certainly know it. They wrote the ToS.
And it isn't just the US. The same principle applies anywhere Proton has a meaningful nexus. Germany where some servers are. The EU under GDPR and the Digital Services Act. The UK under its own post-Brexit surveillance framework. You don't get to selectively invoke Swiss protection for the parts that are convenient while the connections elsewhere quietly do their own work.
Now here's why that clause exists. Because when a US agency comes knocking — FBI, NSA, a state Attorney General, ICE with a subpoena and a willingness to escalate — Proton doesn't have to fight. They don't have to create a diplomatic incident. They don't have to become the next Lavabit.
(Lavabit was an encrypted email service that shut down entirely in 2013 rather than comply with a US government order demanding SSL keys that would have exposed all user data — including Edward Snowden's. The founder chose shutdown over compliance. It became the defining case study in what US jurisdiction actually demands from a privacy service under pressure. Proton invokes Lavabit constantly in their own marketing as the reason Swiss jurisdiction matters. The abortion blog post mentions it by name. Keep that in mind.)
They can point to section 13 and say: our US users already consented to US legal frameworks. Here is the mechanism. We built it in ourselves.
Quiet. Clean. No headlines.
And the blog posts about Swiss sovereignty keep publishing while the compliance happens in the background.
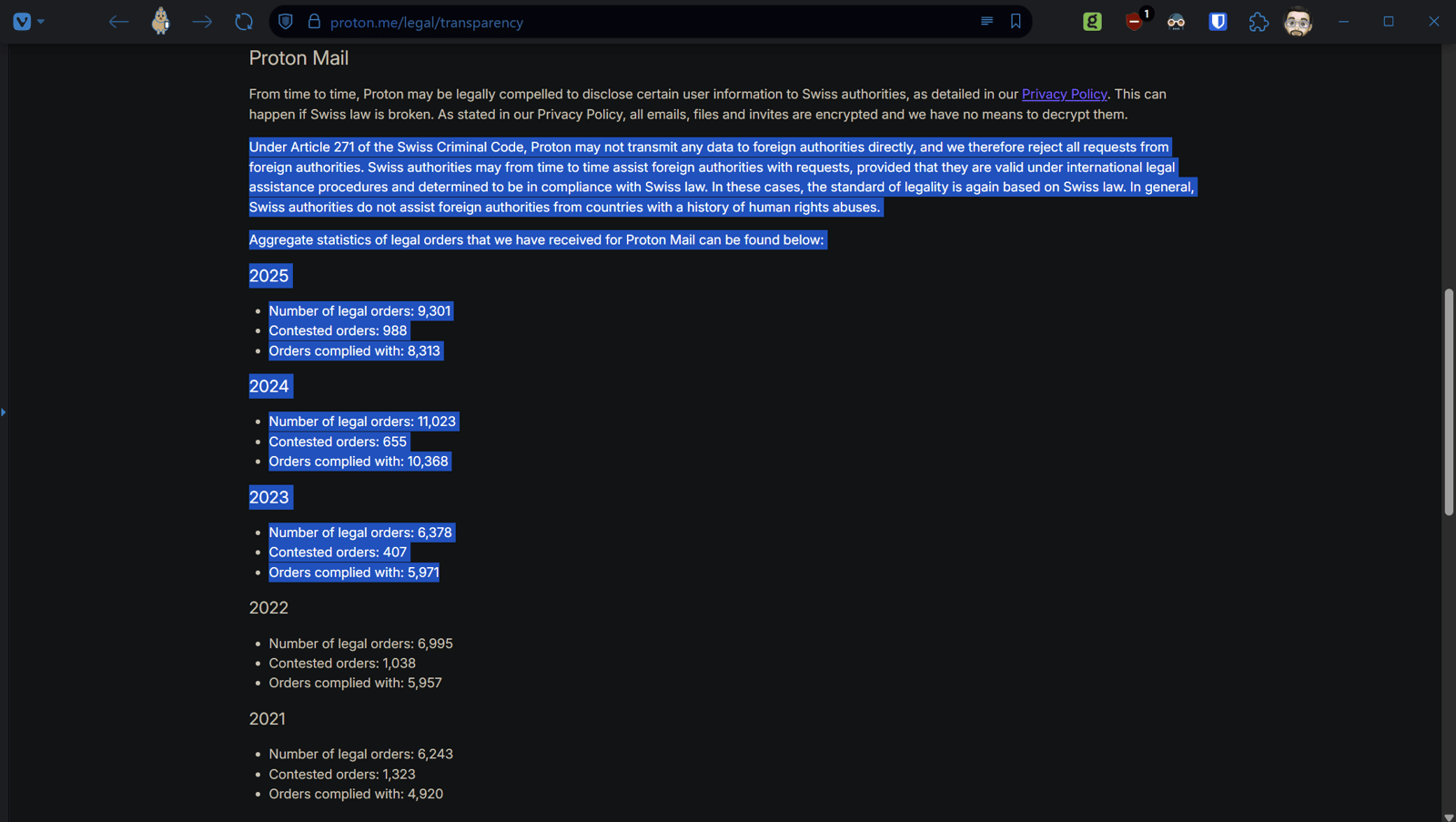
Remember that transparency report? In 2024 alone Proton received 11,023 legal orders and complied with 10,368 of them. 2025 isn't far behind — 9,301 orders received, 8,313 complied with.
But here's the part that belongs in its own moment. That same transparency report page — the one showing those numbers — also contains a statement that under Article 271 of the Swiss Criminal Code Proton rejects all requests from foreign authorities directly.
That statement and those compliance numbers are on the same page.
Proton published both of them.
From the company that told journalists they cannot legally comply with foreign subpoenas.
A note worth making here — and this matters for credibility so pay attention. Compliance with a government order doesn't automatically mean your data is readable. Apple complies with warrants but genuinely cannot access on-device encrypted data. Signal complies with legal process and has essentially nothing to hand over because of how they've architected their systems. The technical design can make compliance largely pointless.
That's a real and important distinction.
The problem with Proton isn't purely that they comply. It's that they told you compliance was legally impossible for them while quietly building the legal framework that makes it straightforward. The question of whether that compliance yields anything useful depends on the specific product, the specific data requested, and the specific technical architecture at that moment.
What isn't in question is whether the mechanism exists. It does. Proton built it themselves. And they didn't tell you.
Before you say "this applies to every company" — I know. That's what I just said. The question isn't whether this is normal. The question is why Proton told you it wasn't.
Google never told you they were outside US jurisdiction. Meta never claimed Swiss sovereignty. Microsoft never said not even government agencies. Mullvad never pretended Swedish law doesn't apply to them. Tuta never claimed to be beyond German courts. Every one of those companies is subject to their own national laws and none of them pretended otherwise. You knew what you were getting.
And yes — every mostly lawful company receiving a valid legal order complies with it. That's not the scandal. That's just how operating in a society with laws works. The scandal is that Proton built an entire premium brand specifically on the claim that they uniquely couldn't be made to comply. And then complied. Over ten thousand times in 2024 alone.
They charged you extra to be different.
And quietly stayed the same.
The question isn't whether this is normal.
The question is why Proton told you it wasn't.
Now let's talk about what this actually means for real people. Because this is where it stops being a legal and technical story and becomes something considerably more human.
THE PRACTICAL LAYER: What This Means For Real People
Everything so far has been documents. Legal language. Infrastructure diagrams. Sub-processor lists. Important — but abstract.
This section is about people.
Let's start with the most straightforward scenario. A US citizen under investigation for something. Doesn't matter what. The investigation exists and they've been using Proton.
The investigating agency doesn't need to fight Proton's encryption. They don't need a Swiss court order. They don't need to create a diplomatic incident. They have several paths that exist entirely outside Proton's control:
ISP records showing every connection to Proton's servers. When. From what IP. For how long. If you're a US user that's your ISP under US jurisdiction directly. If you're elsewhere your ISP may operate under different jurisdiction — but that doesn't mean you're clear. The reach doesn't stop at any one border.
Intelligence sharing agreements, Interpol channels, bilateral law enforcement frameworks, and mutual legal assistance treaties mean any sufficiently motivated agency — US, UK, EU member states, and frankly some considerably less comfortable names on that list — can request connection data through official channels regardless of where your ISP physically sits.
Five Eyes countries share intelligence routinely and extensively. Fourteen Eyes extends that further. And beyond formal agreements there are informal channels that don't require treaty frameworks at all — just a working relationship between agencies and a request that gets honored.
The architecture doesn't care who's asking. It just sits there. Accessible. To whoever has the right paperwork or the right relationship with someone who does.
And if the thought of US agencies having that access is uncomfortable — spend a moment considering that the same infrastructure, the same channels, the same bilateral frameworks are available to governments whose human rights records you probably don't want anywhere near your call metadata either.
That's not hypothetical. That's how intelligence and law enforcement cooperation actually works in 2026.
Payment records. If you paid for Proton with a credit card through Stripe or Chargebee — both US companies — your real identity is attached to that account regardless of what username you chose. No encryption protects a billing record.
And yes — ironically the Gmail user who never thought twice about privacy may in some cases be more efficiently surveilled through commercial data purchases than through legal process. Google's business model is surveillance capitalism. The data already exists, already packaged, already purchasable. Why file a subpoena when you can just buy it? No legal threshold required. No notification ever. Proton told you they were categorically different from that. The infrastructure suggests the gap is narrower than advertised.
LiveKit's call detail records. Sitting on US infrastructure. Under US jurisdiction. Accessible without notifying Proton. Your IP address, connection timestamps, and call metadata from every Proton Meet session you've ever had.
Mobile app store records. If you downloaded Proton's apps through Apple's App Store or Google Play — both of which comply extensively with government requests — your real identity is tied to that download.
Device seizure. If your device is in hand and you're logged in — and most people are always logged in — the encryption argument collapses entirely. The app already decrypted everything locally. They're reading your screen effectively. And forensic tools like Cellebrite can extract data from many devices without even needing a passcode.
We've all seen the scene. Frantic deletion. Factory reset. Phone in the toilet. The assumption is always the same — delete it and it's gone. Earlier this week a federal courtroom in Texas demonstrated otherwise.
The FBI presented evidence in a recent trial that they recovered deleted Signal messages from a defendant's iPhone. Not by breaking Signal's encryption. Not by going to Signal. By extracting Apple's internal notification database, which had cached incoming message content because the user had notification previews enabled. Signal was deleted. The messages were still there. In Apple's infrastructure. Which Signal doesn't control and never did.
The secure app did exactly what it promised. The layer underneath it did something else entirely.
Sound familiar.
And for anyone reading this who thought privacy tools were a way to get away with something — this would be a good moment to reconsider your life choices. The point of this piece is that innocent people are exposed by these gaps. The irony is that the gaps catch the guilty ones too. The infrastructure doesn't discriminate.
If this dynamic feels familiar it should. The gap between what a privacy promise implies and what the infrastructure underneath actually delivers has been documented in this series before. The Apple piece covered it. The Signal case this week lives in exactly that gap. The secure app did its job. The layer underneath did something else. Same pattern. Different company. Different product. Same gap.
And here's the one most people don't think about.
You don't have to be the target.
Modern digital investigations don't start and end with one person. They pull threads. They look at everyone who interacted with the target. Everyone in the same spaces. Everyone whose IP hit the same infrastructure around the same time. Metadata makes this trivially easy because you don't need content — you just need connection records.
Which means the person who:
- Replied to a post that's now part of an investigation
- Boosted something on Mastodon from an account under scrutiny
- Was in the same Discord server
- Followed the same subreddit being monitored
- Had a Proton Meet call with someone three degrees removed from the actual target
- Was browsing a forum that touched on something an agency was already watching
...can find themselves in a metadata dragnet without ever being suspected of anything. They just happened to be in the same digital spaces at the same time.
And their content — their private conversations, their calls, their emails — gets swept up in that net. Reviewed. Potentially retained. Potentially shared with other agencies under joint investigation frameworks. Long after the original investigation closes.
The "not relevant" determination happens after it's already been collected. After it's been seen. After it's potentially been passed along. The privacy violation already occurred the moment it was swept in. Relevance only determines whether it gets used in court — not whether it was seen, stored, or shared.
You don't get notified. You don't get to contest it. You find out years later if ever.
And this isn't theoretical. Agencies operating under US jurisdiction seek data through US infrastructure channels routinely. That's not a political statement. It's a matter of public record. Documented by Reuters, the Associated Press, court filings, government contracts made public through FOIA.
Which brings up something worth saying plainly. The same architecture doesn't distinguish between a legitimate targeted investigation and someone with sign-off and a hunch and an axe to grind. The oversight mechanisms that are supposed to prevent abuse are the same ones that have repeatedly failed to prevent it historically. COINTELPRO. NSA bulk collection. FBI surveillance of journalists. The history is not short.
And the bar for "enough cause" shifts with the political environment. It shifts with who's in office. It shifts with which agencies have expanded mandates. It shifts with what gets defined as a person of interest on any given day.
From the outside, having nothing to hide and having something to hide can look exactly the same. Investigative instinct doesn't come with a filter for intent. It comes with a mandate to follow the anomaly. And in a surveillance landscape optimized around big tech norms, choosing privacy is the anomaly.
The person who doesn't use Facebook. Who uses a VPN. Who has a Proton email. Who uses Signal instead of iMessage. Each one individually completely reasonable. Stacked together they start to look like a profile to someone whose job is finding profiles. Not because the person is guilty. Because the pattern stands out.
And even when it gets run all the way through and amounts to nothing — even when the determination is effectively "what a weirdo, nothing here" — it didn't end cleanly. The inquiry exists in a file. The data pulled exists in retention. The analysts who touched it have seen it. It may have been shared laterally before anyone determined it was nothing. Future inquiries by different agencies may surface the old one and treat its existence as prior interest rather than a cleared matter.
Regulatory retention schedules are not short. Federal records minimum five years. National security adjacent material potentially decades. Some intelligence contexts indefinitely.
It's not unlike what happens when a search warrant kicks in the wrong door. The door gets repaired eventually. The data doesn't get unread. The file doesn't get unfiled. The weirdo with wedding pictures has a file now. It'll be there longer than the investigation that created it.
Now let's talk about what this means in practice. Not hypothetically. In a federal courtroom. On the record.
In March 2026 — weeks before this piece was written — court records reviewed by 404 Media revealed that Proton Mail provided payment data for an account linked to the Stop Cop City protest movement in Atlanta to Swiss authorities, who then handed it to the FBI through a Mutual Legal Assistance Treaty. The account was associated with the Defend the Atlanta Forest group. The FBI's request was filed by a Domestic Terrorism squad special agent. The payment data — a credit card identifier — was enough to identify the real person behind the anonymous account.
As of this writing no charges have been filed against them.
They were just identified. By a Domestic Terrorism squad. Using data from the Swiss privacy company that told them they were protected.
Proton's official response deserves to be noted precisely because it is so carefully worded. Their head of communications stated publicly that Proton did not provide information directly to the FBI — the data went to Swiss authorities first, who then passed it to the FBI through the Mutual Legal Assistance Treaty process.
Technically accurate. And completely missing the point.
They gave it to the people who gave it to the FBI. Through a process that exists specifically to give foreign law enforcement access to data held by Swiss companies. That is not a meaningful distinction for the person whose identity just landed in a federal affidavit.
And it wasn't the first time. This marks Proton's third known disclosure to authorities. A Catalan independence activist whose recovery email was handed over. A French climate activist whose IP address Europol compelled Proton to log — despite their claims of not logging IPs by default. And now a Stop Cop City protester whose payment data traveled from Proton's servers through Swiss courts to the FBI.
Three cases. Three activists. Zero broken encryption. The email content stayed private every time. The metadata did not.
The Swiss court wasn't a shield. It was a processing step. The FBI asked. Switzerland evaluated. Switzerland said yes. Proton complied. The data moved. The user was identified. No charges filed.
That is what "only governed by Swiss law" looks like in practice.
Now let's talk about the EU user who thinks GDPR has them covered.
They go to exercise their right to erasure. Right to access. Standard GDPR tools that EU citizens have real legal recourse to use.
And they find:
Proton doesn't have that data. LiveKit does. LiveKit is a California company outside GDPR's direct enforcement reach. The data is physically on US soil. The EU has no meaningful enforcement mechanism against a US company without substantial EU operations to attach to. And even if they did — national security collection exemptions exist specifically to carve out exactly this kind of data from GDPR rights.
There is no door to knock on. Their statutory rights — real rights, with real legal teeth — evaporate at the infrastructure layer.
And then there's the Swiss citizen.
A Swiss citizen. Living in Switzerland. Using a Swiss company. Protected by Swiss law. Possibly with GDPR rights as an additional layer. Who read nothing in Proton's marketing that suggested any of this. Who may have specifically chosen Proton because they wanted Swiss legal protection and believed they had it — or simply wanted to support a European privacy-focused company rather than feeding more money into US big tech. Either reason is completely legitimate. Neither one changes what the infrastructure actually delivers.
Their Proton Meet call routed through Oracle infrastructure in Phoenix, Arizona. Their metadata sitting at a California company that explicitly cooperates with US law enforcement. Their connection records accessible without notifying Proton. Their GDPR erasure rights functionally worthless against US infrastructure.
And the first they know about any of it is when someone shows up asking about a conversation they had months ago. That they thought was private. That they had specifically because they believed they were protected.
Under a national security framework they may never be told why. The agency doesn't have to tell Proton. Proton doesn't have to tell the user. LiveKit certainly doesn't. The Swiss citizen becomes a data point in an American investigation they have no knowledge of, no standing in, and no rights within.
That is not a hypothetical edge case.
That is the architecture working exactly as designed.
And it gets worse.
Remember that journalist page. The one with the discount program. The one that specifically told journalists — people with the highest stakes imaginable — that Swiss jurisdiction meant foreign subpoenas couldn't touch them.
A source who came forward based on that promise. A whistleblower who made the call trusting that assurance. A journalist in a country where their government has friends in Washington. People whose sources don't just risk prison — in some parts of the world they risk disappearing entirely. A dissident. A human rights worker. Someone documenting atrocities who needed to know their communications were genuinely protected before they trusted anyone with information that could get them killed.
All of them potentially on infrastructure that a US agency can walk straight through.
Not because they didn't do their research.
Because they did.
And Proton's own page told them they were covered.
And here's the part that keeps it from ever feeling safely in the past. Even if nothing happens today. Even if no investigation ever targets anyone in that conversation. The data doesn't disappear. It sits. In retention. In logs. In call detail records on US infrastructure.
And one day — could be next year, could be a decade from now — someone files a FOIA request about something completely unrelated. A researcher. Another journalist. A lawyer in a different case. And buried in the documents that come back, partially redacted, formatted in 12 point Courier because that's how government documents look — could be a connection record. An IP address. A timestamp. A call duration.
From a conversation someone had in good faith on a platform that told them they were protected.
They'll never know it happened.
Unless someone shows up at the door.
Or unless they don't.
That page is still up.
The journalist discount is still available.
And the infrastructure hasn't changed.
BEFORE YOU COME FOR ME: The Arguments You're Already Typing
If you've made it this far — and I asked you to, remember — you probably have objections. Good. That means you're thinking critically. That's exactly what this topic deserves.
Let's go through them.
"You're misreading the ToS."
No. The ToS is linked above. Section 13. Last modified March 31, 2026. Read it yourself. The two-tier jurisdiction clause is not ambiguous. It does not require interpretation. It says what it says in plain English. If you believe it means something different than what it plainly states, the conversation is on Mastodon and you're welcome to make that argument. Bring your legal citations.
"The encryption still protects you."
Possibly. Probably even, for content between Proton users. That honest concession was made earlier in this piece and it stands.
But encryption protects content. It does not protect metadata. It does not protect payment records. It does not protect ISP logs. It does not protect call detail records sitting at LiveKit on Oracle infrastructure in Phoenix. It does not protect you from device seizure when you're logged in. And it did not protect the Stop Cop City protester whose payment data traveled from Proton's servers to Swiss courts to a Domestic Terrorism squad at the FBI.
The encryption is the last line of defense being marketed as the whole defense.
"LiveKit is just infrastructure. Proton can't control what they do."
Correct. They can't.
That's the point.
Proton chose that infrastructure. Deliberately. While marketing Swiss sovereignty. While publishing blog posts about being outside US jurisdiction. While selling journalist discounts with promises about foreign subpoenas. The choice of infrastructure is the story. You don't get to build on American servers and then claim Swiss protection for what happens on those servers.
"Proton has fought for privacy. They've taken real stands."
Yes. They have. That was acknowledged at the top of this piece and it remains true.
They challenged Swiss surveillance law and won. They've taken positions on encryption legislation. They've done real work. None of that is in dispute.
But fighting for privacy in the courtroom while quietly building a two-tier ToS and routing your newest product through all-American infrastructure isn't a contradiction that cancels out. It's a contradiction that makes the deception more sophisticated. Not less damning.
You can do good things and still mislead people. Both can be true simultaneously.
"You're just fear mongering."
Every claim in this piece links to a primary source document. Proton's own ToS. LiveKit's own DPA. Proton's own Meet privacy policy. Proton's own transparency report. Proton's own blog posts. Federal court records reviewed by 404 Media.
Not a single anonymous source. Not a single leaked document. Not a single interpretation that required reading between lines.
If the facts are frightening that's a problem with the facts. Not with the reporting.
"This applies to every company."
Yes.
I know.
That's what I just said.
Before you say "this applies to every company" — I know. That's what I just said. The question isn't whether this is normal. The question is why Proton told you it wasn't.
Google never told you they were outside US jurisdiction. Meta never claimed Swiss sovereignty. Microsoft never said not even government agencies. Mullvad never pretended Swedish law doesn't apply to them. Tuta never claimed to be beyond German courts. Every one of those companies is subject to their own national laws and none of them pretended otherwise. You knew what you were getting.
And yes — every company receiving a valid legal order complies with it or fights it in court. That's not the scandal. That's just operating in a society with laws. The scandal is that Proton built an entire premium brand on the claim that they uniquely couldn't be compelled. And then complied. Over ten thousand times in 2024 alone. Three documented times with activists whose anonymity was the whole point.
They charged you extra to be different.
And quietly stayed the same.
The question isn't whether this is normal.
The question is why Proton told you it wasn't.
"You're just trying to destroy Proton."
No. If Proton fixed this — if they rebuilt Meet on genuinely non-US infrastructure, rewrote the ToS to remove the two-tier jurisdiction clause, updated their journalist page to accurately reflect what their infrastructure can and cannot protect against, and published a transparency report that explains the LiveKit relationship honestly — that would be worth writing about too.
And I would write it. Gladly. It might be the shortest post on this site but it would go up. With an update link right back to this piece so anyone who read this one finds their way to it. If they do the right thing they deserve the same public acknowledgment as the receipts that got us here.
This piece isn't about destroying Proton. It's about accountability for a specific set of promises that their own documents — and federal court records — demonstrate they cannot keep.
The difference between those two things is the whole point.
A note — comments are disabled here as they are across the site. Not because I'm avoiding the conversation but because in my experience comment sections are where good faith goes to die. Spam, bad faith, and people who stopped reading at paragraph three tend to drown out anyone with something actual to say.
The conversation lives on Mastodon. Link is in the header. It's open. Anyone can chime in. I'll see it. If you've got a substantive correction, a factual error I missed, or evidence that something here is wrong — bring it there. Publicly. With receipts.
That's how this works.
I'll be there.
THE GAP
Proton is not evil. Say it again for the people in the back — Proton is not evil.
They built real things. They fought real fights. They attracted brilliant people who genuinely believed in what they were building. The encryption is probably real. The intentions may well be genuine. The CERN origin story is not a myth.
None of that is the point.
The point is this.
Somewhere between the particle physics lab in Geneva and the journalist discount page and the "not even government agencies" marketing copy and the California company routing every Proton Meet call through Oracle infrastructure in Phoenix — something went wrong. Or something was always wrong and the marketing just got ahead of the reality. Either way the gap exists. And the gap is documented. In their own words. In their own documents. In federal court records. Linked throughout this piece.
A Swiss citizen used a Swiss company because a Swiss company told them they were protected by Swiss law. Their call went to Arizona.
A journalist trusted a promise made on a page specifically designed to earn that trust. A source made a decision based on that promise. In some countries that decision carries consequences that don't have legal remedies. That page is still up. That promise is still being made. Today. Right now. While you're reading this.
A Stop Cop City protester used Proton Mail for their organizing account. Their payment data traveled from Proton's servers through Swiss courts to a federal Domestic Terrorism squad. No charges were filed. They were just identified. The Swiss court wasn't a shield. It was a processing step.
An ordinary person — not an activist, not a whistleblower, not anyone doing anything wrong — had a conversation in a digital space that later brushed against an investigation they knew nothing about. Their data got swept into a net. Reviewed by someone they'll never know about. Possibly retained. Possibly shared. Possibly sitting in a file somewhere waiting for a FOIA request that surfaces it a decade from now in a document nobody was looking for.
They switched to Proton because someone told them to. Because it was the answer. Because the privacy community had decided it was safe. Because the marketing said Swiss. Because they did everything right.
And "private" meant something specific when they made that choice. It meant protected. It meant outside the reach of the thing they were worried about. It meant the promise on the page.
It didn't mean "probably encrypted at the content layer subject to metadata exposure via a California sub-processor operating as independent Controller under their own DPA with telemetry always routing to the United States regardless of selected region and a two-tier ToS with Federal Arbitration Act provisions for US consumers and a class action waiver buried in section 13 and a Swiss court that evaluates MLAT requests from federal Domestic Terrorism squads and says yes."
That's what private meant to them.
That's not what Proton built.
And the privacy community — the one that answers every "what should I use instead" question with Proton — deserves to know the difference between those two things before they make that recommendation again.
Not because Proton is the enemy.
Because the people asking that question are trusting the answer with something real.
Their safety. Their sources. Their private lives. Their assumption that when a company says private — they mean it.
That assumption deserves better than a Terms of Service clause nobody read and an Oracle server in Phoenix nobody knew about and a Swiss court that forwarded the file.
They charged you extra to be different.
They quietly stayed the same.
And somewhere right now a journalist is recommending Proton to a source who needs to believe the answer is safe.
That page is still up.
Part of the Big Tech's War on Users series.
Find me on Mastodon: @[email protected]
Screenshots of Proton Quotes: